Filter News

Raysync News
February 21, 2024Raysync Cloud: A High-Speed File Transfer Cloud Service
High-speed file transfer cloud service - Raysync Cloud is newly launched!
Raysync News
December 29, 2022Raysync 100-day Program Released! To Build a High-speed Channel to the Data Transfer
Today is the day! Raysync's 100-day program has fully launched. Raysync has introduced a special offer for all of you who have the file transfer needs. Apply now and you 'll get a 100-day free trial of Raysync Pro (3TB transfer volume) that worths $820.

Industry news
December 29, 2022Enterprise Bonus! Say Goodbye to Large File Transfer Anxiety
The transmission tools have been put in place to help enterprises easily cope with the problems of large file transmission, massive small file transmission, slow, latency and packet loss of transnational file transmission.

Raysync News
December 29, 2022Annecy Festival 2021 | Raysync Awaits you in Stand NO – 006!
If you want to learn more about how Raysync works, we invite you to e-meet us at stand NO – 006 from June 15th to 18th in Annecy 2021!

Case Studies
December 29, 2022Case Study: Raysync & A Cloud Solution Provider
Raysync acts as a storage container for enterprise data backup and file synchronization. The Raysync admin console is deployed in Montreal where the data center located.

Raysync News
December 29, 2022What's New in Raysync V5.0.8.8?
Raysync optimizes the file uploading function, and the new version supports selecting files and folders to upload at the same time, making it easier for users to operate and use.

Industry news
December 24, 2022What Technology does Raysync Adopt to Transfer File Cross-border?
Cross-border file transfer and transnational transfer have to face the network transfer environment of ultra-long distance and weak network. If you want to transfer files fast, read on to learn how professional file transfer software Raysync transfers.

Q&A
December 24, 2022[2024] Full Guide - FTP (File Transfer Protocol)
What is FTP?The importance of FTP and how it works? What are some common transfer protocols, click on this article to learn more!

Industry news
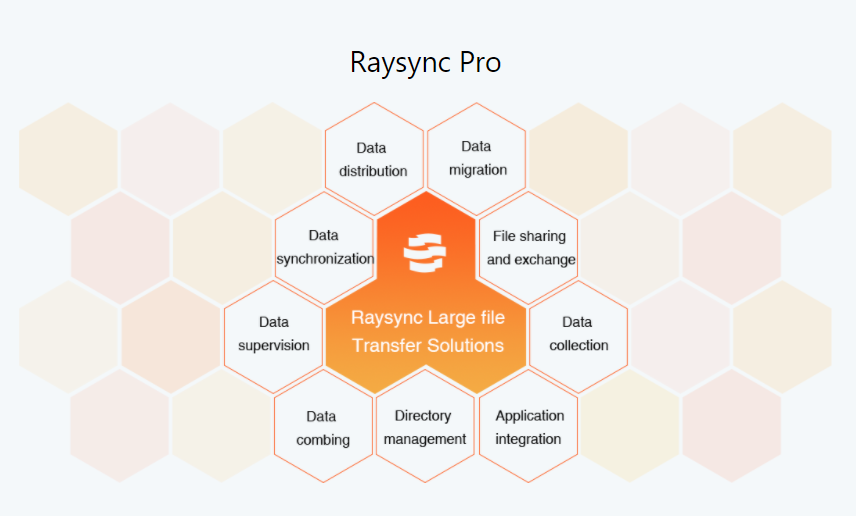
December 24, 2022Introducing You Raysync High-speed Transfer Protocol
RaySSH acceleration tool with Raysync, which integrates the function of Raysync transmission protocol and perfectly replaces ssh/sshd/scp/rsync tool of openSSH, is a special and efficient transmission tool product of Linux/Unix system.

Raysync News
December 22, 2022This Powerful Data Transfer Solution is Used by 99% of Companies
It's time to adopt a more modern and powerful data transfer solution. As time goes by, your company will benefit from this, operate within the scope of compliance standards, and become more efficient after the final rest of FTP.