Filter News
Raysync News
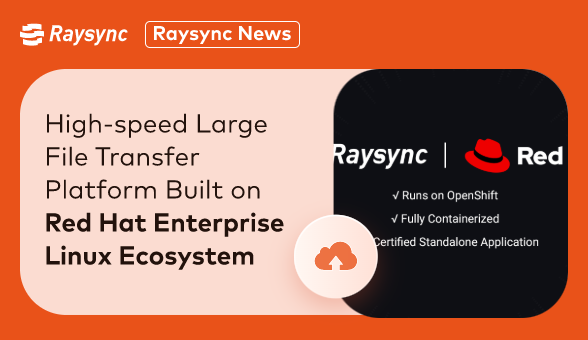
September 11, 2023Raysync, a leading provider of high-performance file transfer solutions, has announced a strategic partnership with Red Hat, the world-renowned open-source software and solutions provider.

Industry news
September 4, 2024Learn how it differs from FTP, see it in action with FileZilla, and explore top SFTP transfer tools for business.

Industry news
September 4, 2024Everything you need to know about SmartFTP Enterprise. Learn about its features, pros and cons, alternatives, and whether it’s the right FTP solution for you.

Industry news
August 29, 2024Discover the top 5 enterprise secure FTP solutions to elevate your business.

Industry news
August 29, 2024Discover the 7 fast file transfer software utilities that prioritize speed and efficiency for both individual users and businesses.

Industry news
August 29, 2024Discover the fastest FTP client for your needs in 2025. Compare FileZilla and Raysync to find out which tool offers the best speed and performance.

Industry news
August 29, 2024Discover 5 easy ways to send large files fast without hassle, including free options.
![Top 7 Large File Transfer Services [Latest Update]](http://images.ctfassets.net/iz0mtfla8bmk/IDPUTyroYc6ZqDD4a8vIN/f8011e72259ca948035e0867a94beb75/large-file-transfer-service.png)
Industry news
August 16, 2024Discover the best large file sharing services for both personal and business use, and find out which service offers the most value for transferring big files.

Industry news
August 16, 2024Explore the ins and outs of FileZilla Pro Enterprise Server, from what it is to how to download it. Also discover top FileZilla alternatives like Raysync.

Industry news
August 15, 2024Explore the full review of the open-source fast data transfer in 2025.