How to Securely Transfer Large Files in 2022
At present, the amount of file-based data in enterprises has increased sharply, but many companies still usually use conventional methods such as email, IM tools, FTP, and network disks for file transfer. When the file capacity increases and the network environment deteriorates, the efficiency of file transfer and data exchange is low, Poor security. If the file is larger, it usually adopts a lower method such as express hard disk, which cannot meet the requirements of the enterprise to obtain the file in time, seriously affects the overall operating efficiency of the enterprise.

In addition, the use of the above-mentioned traditional transfer methods is too decentralized, which is not conducive to the centralized management of enterprises. In the era of cloud computing, enterprises currently have more and more service nodes and storage nodes, and data flow requirements based on business processes and hybrid cloud architecture are also increasing. The lack of an effective file transfer management platform is undoubtedly a major pain point.
Methods for secure transfer of large files
1. CDN Technology
CDN: Content Delivery Network (Content Delivery Network). By adding a new network architecture to the existing network, it is mainly composed of two parts, which are divided into two parts: the center and the edge. The center refers to the CDN network management center and the DNS redirection resolution center, which is responsible for global load balancing, and the equipment system is installed in the management Central computer room, edge mainly refers to remote nodes, the carrier of CDN distribution, mainly composed of Cache and load balancer. Choose to publish the content of the site to the "edge" of the network closest to the user, so that the user can obtain the desired content nearby, thereby improving the response speed of the user to the site to a certain extent. CDN's data requirements are only independent documents (software, modules, files) or "independently replaceable" document parts.
2. Transfer Technology Based on FTP Protocol
FTP (File Transfer Protocol) is the abbreviation of File Transfer Protocol. FTP allows files to be shared between hosts and is used to control the two-way transfer of files on the Internet. It is a C/S system. FTP uses different port numbers to transfer different content, and different TCP connections are established. First, use TCP to generate a virtual connection for transmitting control information, and then generate another connection for data transfer. Combined with the FTP protocol, file (compression/decompression) or file (fragmentation/assembly), file verification and other technologies can be used, and large files can also be transferred. FTP transfer software such as (FileZilla) also has the ability to manage users, block or filter designated IP addresses, Port, control user upload and download speed, detailed transfer history, and log, and can also carry out the encrypted transfer of data. It has the advantages of ensuring transfer security and protecting personal privacy.
3. Transfer Files Based on Middleware
Use MQ, MT, and other middleware to transfer files, with functions such as data compression, large file transfer, and breakpoint resumable transfer. The transfer of large files uses BlobMessage, an efficient process that uses fileserver to transfer. Message middleware technology has two core functions: asynchronous and decoupling. These two core functions improve the working efficiency of the application system as a whole, enhance the usability, stability, and scalability of the system, and can realize the safe and reliable transfer of large files.
4. IM Instant Messaging Technology
Instant Messenger (IM) technology is mostly based on TCP/IP and UDP for communication, and TCP/IP and UDP are communication transfer protocols based on the lower-level IP protocol. The former is through the form of the data stream, after dividing and packaging the transmitted large file data, through the virtual-circuit connection established between the machines, a continuous, two-way transfer protocol that strictly guarantees the correctness of the data is carried out, mainly Reliable transfer is achieved through mechanisms such as checksum, serial number, confirmation response, timeout retransfer, connection management, and window sliding. The latter is a connectionless transport layer protocol in the OSI reference model, which is mainly used for non-required In the transfer of data packets arriving in sequence, the inspection and sorting of the packet transfer sequence are completed by the application layer, providing simple and unreliable transaction-oriented transfer services. Because of its fewer control mechanisms, the delay in the transfer of data is small, and the transfer is efficient. IM technology mainly combines the respective advantages of the two to highlight the characteristics of immediacy and accuracy of transfer, but there are still certain technical difficulties in the application of large file transfer.
Based on the problems and status quo that most companies are facing to transfer large files, and based on the analysis of the characteristics of the original mainstream transfer technology, the foundation to ensure the secure transfer of large file lies in the development of the transfer software that can have the advantages described in the third party. At the same time, it can solve the technical difficulties of the current large file transfer.
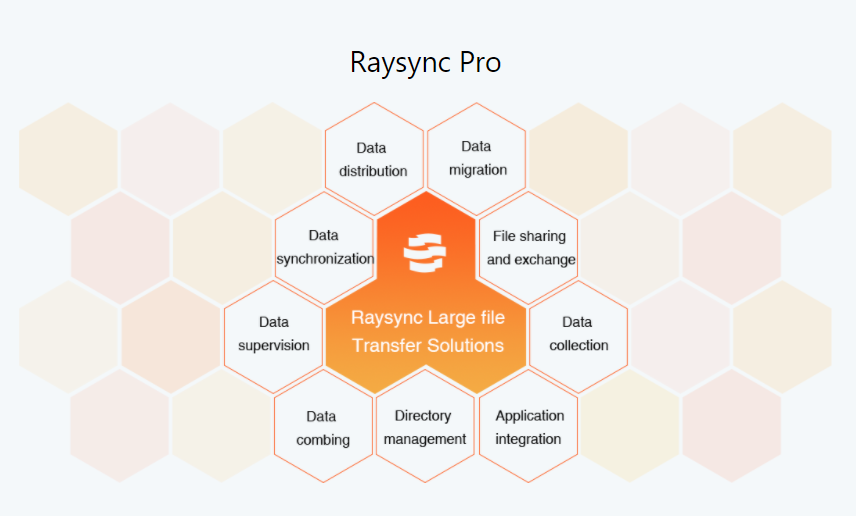
In order to ensure the security of transmitted data and prevent data leakage, cracking, monitoring and other security issues, Raysync strengthens internal data communication security management and control, adopts online banking-level AES-256 encryption technology, and uses SSL encryption during transmission to effectively ensure data security. At the same time, Raysync uses access permissions and OS permissions settings to achieve more stringent access control.
Raysync adopts an integrated security management mode to conduct unified management and monitoring of various file data, data types, user behavior logs, etc., analyze and warn security risks in an all-round way, and effectively conduct data risk management.
You might also like

Raysync News
February 4, 2024How to solve the problem of inefficient data transfer in the automotive industry?
How to effectively improve the efficiency of data transmission in the automotive industry is not only related to the productivity of enterprises, but also affects the progress of the whole industry.
Raysync News
December 29, 2022Raysync 100-day Program Released! To Build a High-speed Channel to the Data Transfer
Today is the day! Raysync's 100-day program has fully launched. Raysync has introduced a special offer for all of you who have the file transfer needs. Apply now and you 'll get a 100-day free trial of Raysync Pro (3TB transfer volume) that worths $820.

Raysync News
July 10, 2020Raysync: An IT personnel perspective
Raysync software provides a stable and reliable file transfer solution. The ability to transfer large files to global locations is a major challenge.