Raysync Security Design: Web Security
December 9, 2020As a file acceleration transmission software, for the convenience of users, Raysync can be accessed directly on the web. The browser supports the convenient process of interactive operation, and we should strictly control the security of the browser.

In the data transmission, we can simply divide the web into several layers:
Browser: Browser is the client, which provides data information interaction between the client and the server;
Http: When the client interacts with the webserver, there is a web request, which is based on the unified application layer protocol-HTTP protocol to exchange data. HTTP is a lightweight protocol, which requires no connection and provides fault tolerance for communication errors.
Middleware: Middleware is a general service between platform (hardware and operating system) and application.
Server container: Server container is responsible for parsing user requests and scripting languages, such as Tomcat and JBoss. When we visit the web page, we see the content processed by the web container;
Database: Dynamic pages can provide interactive information query service, which mainly depends on the realization of web databases. Web pages containing forms are provided as access interfaces, and query results are also returned to users in the form of Web pages containing data lists.
In view of the above points, the design of Raysync on web security:
User-side Web portal and management-side Web Portal support access IP address isolation and port isolation;
Support some nodes to disable user plane Web Portal or management plane web portal;
Support HTTP and HTTPS, and the administrator can disable HTTP and only expose Https service;
HTTPS TLS 1.1, TLS 1.2, TLS 1.3, only open the encryption algorithm suite recognized by the industry as safe;
On the Web page of Raysync login, the effective range of session is only valid for the current access page, completely eliminating CSRF cross-site attack;
Before each version of Raysync is released, professional Web vulnerability scanning service will be used to scan vulnerabilities and repair the latest released vulnerabilities in time.
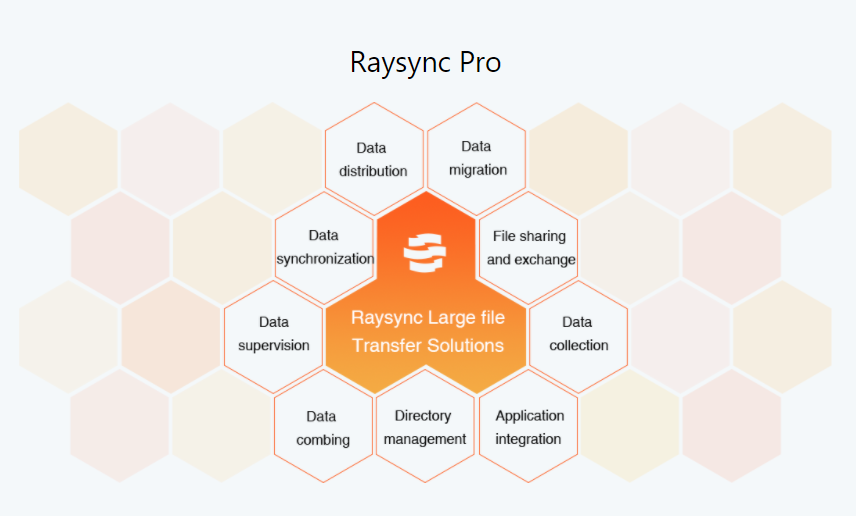
As a one-stop solution provider, Raysync has independently developed its core transfer technology with its professional technical teams to offer high-performance, secure, and reliable large file transfer and file management services for major enterprises.
You might also like
Raysync News
November 17, 2023Data synchronization is crucial for businesses to ensure unified and consistent data everywhere. Keep reading to learn about its importance, challenges, and best data sync software.
Raysync News
December 29, 2022Today is the day! Raysync's 100-day program has fully launched. Raysync has introduced a special offer for all of you who have the file transfer needs. Apply now and you 'll get a 100-day free trial of Raysync Pro (3TB transfer volume) that worths $820.

Raysync News
January 5, 2024Facing major challenges in the healthcare sector, RaySync is empowering the modern and rapid development of data transfer in the healthcare industry.